A New Frontier in Phishing Campaigns
Cybersecurity researchers have uncovered a new and alarming evolution in phishing tactics—one that allows attackers to completely evade traditional defenses, remain virtually undetectable, and leave no digital trace.
Criminal groups are now exploiting legitimate services such as Ngrok, Cloudflare’s Argo Tunnel, and URL shorteners like Bit.ly to host and distribute phishing content in ways that are nearly impossible to monitor using conventional tools.
How the Attack Works: Down the Reverse Tunnel
Unlike traditional phishing that relies on registered domains and cloud-hosted websites, this emerging threat uses a combination of reverse tunneling and URL obfuscation:
- Phishing pages are hosted locally on attackers’ machines.
- Reverse tunneling services (like Ngrok or Argo Tunnel) expose these local servers to the internet via temporary, random URLs.
- URL shorteners mask the tunnel-generated links, making the phishing attempt look legitimate and difficult to analyze or trace.
- Attackers distribute the links through channels like SMS (smishing), email, or instant messaging platforms.
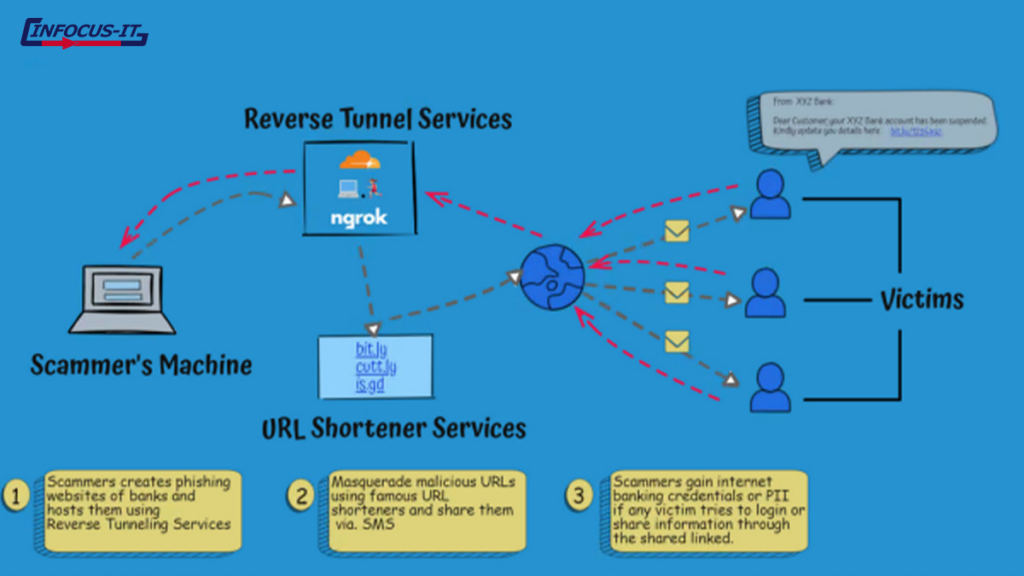
Because these URLs are often active for just 24 hours, the threat is short-lived but extremely effective—and difficult to stop in time.
“We started noticing patterns of such abuse during our routine monitoring of client-related assets and data,” said INFOCUS-IT. “Reverse tunnel attacks have become quite common these days.”
A Global Threat Targeting Major Brands and Institutions
Initially observed in phishing campaigns targeting Indian banking customers, this technique has since been spotted across the US, UK, and Europe—with attacks aimed at major global brands, financial institutions, and even government services.
Victims are being lured into handing over:
- Banking credentials
- Aadhaar (Indian national ID) numbers
- Sensitive personal information
The misuse of legitimate tunneling tools removes the need for attackers to register domains—bypassing brand impersonation filters, hosting provider takedown protocols, and DNS monitoring.
Why It’s So Hard to Detect
Reverse tunnels allow attackers to bypass the three main detection pillars used in anti-phishing systems:
1. Hosting Detection
Traditional phishing relies on suspicious domains hosted on cloud or VPS providers, which can be blocked or taken down. Reverse tunnels eliminate the need for external hosting altogether.
2. Domain Name Filtering
Malicious domains often include keywords related to brands or services they impersonate. Attackers now use random or generic URLs, making it hard to flag them for brand infringement.
3. Attribution and Forensics
Since the phishing content is hosted locally, and the URL is temporary, there’s little to no evidence left after the attack window closes.
“If a domain is registered with a hosting provider, they can respond to takedown requests. But with reverse tunnels, the provider has no accountability,” explains Chris Preece, Head of Cyber Operations at Protection Group International.
Countermeasures: What Can Be Done?
Although this technique is stealthy, organizations are not powerless. Here’s how security teams and businesses can respond:
1. Monitor Reverse Tunnel Service Usage
- Services like Ngrok now require users to register and share IP addresses before hosting public-facing content.
- Enterprises should keep an eye on traffic patterns involving these services and block unnecessary access from corporate networks.
2. Implement Behavioral Analysis
- Use advanced threat detection tools that flag unusual outbound connections, including access to suspicious or short-lived URLs.
- Combine with real-time threat intelligence feeds that track abuse of tunneling and URL shortening platforms.
3. User Awareness and Training
- Teach employees and customers to be skeptical of shortened URLs—especially from SMS or email sources.
- Regular phishing simulations can help build instinctive caution in users.
Work With Providers
- Coordinate with URL shortening and reverse tunnel providers to flag and disable malicious links when detected.
- Advocate for better abuse detection and stricter content monitoring from these service platforms.
The Bottom Line: Phishing Is Getting Smarter—So Should We
As reverse tunnel phishing grows in popularity among threat actors, the gap between traditional security controls and modern attack methods is widening. Cybercriminals are innovating with tools that were never designed to be malicious—turning legitimate infrastructure into effective attack vectors.
Now more than ever, security teams must stay proactive, double down on user education, and adapt their detection strategies to this new wave of covert phishing campaigns.
“Effectively, this is just another channel for phishing—but the difference is attribution. And that makes all the difference,” says Preece.
Final Recommendation
- Stay updated with emerging threats.
- Reassess your phishing defense stack.
- And never underestimate the power of a well-crafted, shortened URL in the hands of a cybercriminal.
Got thoughts or questions about reverse tunneling in phishing attacks? Leave a comment below or subscribe to our newsletter for more deep-dive cybersecurity insights.
At INFOCUS-IT, we specialize in advanced cybersecurity solutions—from threat detection and incident response to compliance and risk management. Whether you’re a small business or a large enterprise, our experts are here to protect what matters most.
Book your vulnerability scan now → infocus-it.com
📩 Support: support@infocus-it.com
📞 Helpdesk: +91-8178210903
hashtag#vapt hashtag#owasp hashtag#bugbounty hashtag#ethicalhacking hashtag#infocusit